Intelligent Choice: The Business Benefits Of Using RingCentral
When it comes to technology investment, the bottom line is always going to be the return. in quantified form. If you’re building a business case for UCaaS and CCaaS adoption, this is a good place to start. Download to read more now!

Communications And Worker Productivity: Where We Are Today
Five years ago, we teamed up with research firm CITE to investigate the roadblocks to workplace productivity. At that time, many workers were overwhelmed by the volume of workplace communication and workplace tools they juggle every day.
Integrating Unified Communications and Contact Center
One of the biggest trends in the enterprise communications area today is the integration of unified communications-as-a-service (UCaaS) and contact center-as-a-service (CCaaS). Businesses are taking this step to improve both the customer and employee experience.
How to Improve Your Customer Experience by Elevating Your Employee Experience
Don’t let low employee engagement hurt your customer service. Equip your team with the right tools, like an integrated cloud communications and contact center solution, and they’ll be able to provide your customers with outstanding service every time.
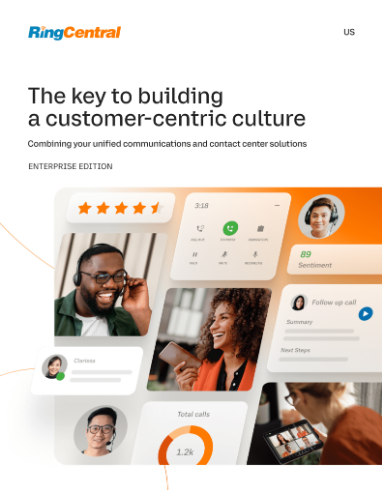
The Key To Building A Customer-Centric Culture: Combining Your Unified Communications And Contact Center Solutions
In fact, 80% of customers now view customer experience as being of equal importance to the products the company sells.1 With the importance of customer retention, it’s also worth noting that 91% of customers are likely to make repeat purchases with a company that provides positive experiences.

How RingCentral Helped These 6 Companies Better Serve Their Customers
Find out how these six organizations built stronger customer relationships from one deeply-integrated, unified communications and customer service platform.

CIO Guide: 4 Steps To A Risk-Free Cloud Migration
Cloud technologies, and cloud telephony specifically, have matured greatly—richer functionalities, stronger security, better uptime, and enhancements to user experiences. The result is a market in transition, with businesses moving from data centers to the cloud at a rapid pace. But despite the meteoric rise, the truth is that the majority of enterprise communications today remain on-premises.
The Shifting Paradigm Of The CIO
In the ever-changing landscape where technology and business intersect, the CIO is no longer just a guardian of information systems, but a catalyst for innovation and a strategist shaping their enterprise. Their responsibilities now extend to orchestrating digital ecosystems, fortifying cybersecurity, and integrating emerging technologies like AI and blockchain into business operations.